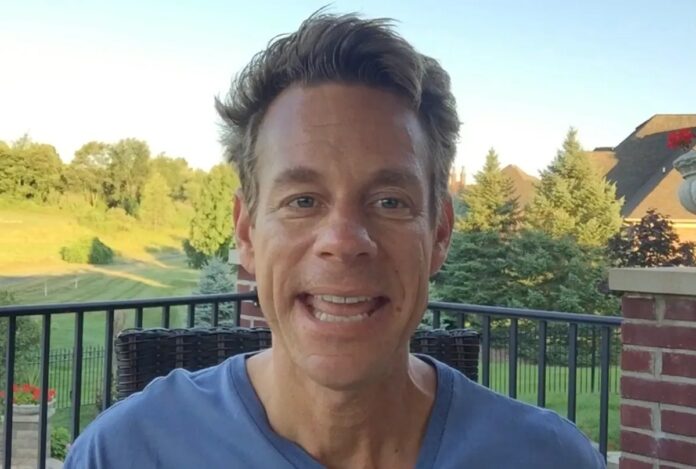
In a significant legal development for the cybersecurity landscape, Bryan Fleming, the founder of the surveillance software company pcTattletale, has avoided prison. On Friday, a San Diego federal court sentenced Fleming to “time served” and a $5,000 fine, following his guilty plea to federal charges related to the operation of his spyware business.
A Milestone in Federal Prosecution
This case is notable not just for the sentence, but for its precedent. Fleming is the first spyware maker to be successfully prosecuted by the U.S. Department of Justice since 2014.
While many actors in the “stalkerware” industry operate from overseas to evade law enforcement, Fleming’s operations were conducted within the United States. This made him a direct target for Homeland Security Investigations (HSI), marking a clear signal that the U.S. government is renewing its focus on domestic operators of illegal surveillance tools.
The Mechanics of “Stalkerware”
The software sold by pcTattletale falls into a category known as “stalkerware.” Unlike legitimate enterprise monitoring tools, these consumer-grade apps are designed to be planted on a device—such as a smartphone or laptop—without the user’s knowledge or consent.
Once installed, the software stealthily monitors and uploads sensitive data, including:
– Private messages and emails
– Personal photographs
– Real-time GPS location
Federal investigators revealed that Fleming did not merely provide the tool; he knowingly assisted customers in spying on non-consenting adults, including domestic partners and others outside of an employment context.
Security Failures and Data Exposure
The downfall of pcTattletale was accelerated by severe security negligence. Investigations and security researchers highlighted two major crises that compromised the privacy of both the perpetrators and their victims:
- Public Exposure: A security flaw was discovered that exposed millions of screen captures to the open internet. This meant anyone could potentially view the live contents of a victim’s screen, including sensitive data from hotel guest computers.
- Massive Data Breach: Following a high-profile hack and website defacement in 2024, a breach revealed that over 138,000 customers had used the service. The hack granted access to files stored in pcTattletale’s cloud storage, exposing the very data the software was designed to steal.
Despite these breaches, Fleming reportedly did not notify his customers or the victims whose data had been compromised, claiming he “deleted everything” from his servers following the incident.
Why This Matters
The sentencing of Bryan Fleming serves as a litmus test for how the U.S. government will handle the growing market of consumer-grade surveillance technology. While the $5,000 fine and “time served” may seem lenient to some, the successful conviction establishes a legal framework to pursue domestic developers who facilitate digital stalking and privacy violations.
The prosecution of pcTattletale signals a shift toward holding the architects of surveillance software—rather than just the end-users—accountable under federal law.
Conclusion
By securing a conviction against a domestic spyware developer for the first time in a decade, federal authorities have set a precedent that could lead to increased scrutiny and legal action against the broader stalkerware industry.